Ledger Login: Secure Access to Your Crypto World
Master the art of safely logging into your Ledger device and managing your digital assets like a professional.
Understanding the Ledger Login Process
In the ever-evolving world of cryptocurrencies, security is paramount. The Ledger login process is at the heart of this philosophy—allowing users to authenticate their wallets securely without exposing their private keys online. Ledger devices, such as the Nano X and Nano S Plus, combine robust hardware security with the user-friendly Ledger Live application to make managing crypto seamless and safe.
When you log in, you are not typing a password into a website; you’re connecting directly to a physical device that holds your cryptographic keys offline. This difference is what separates Ledger from most software-based wallets and exchanges, which remain vulnerable to online attacks.
How to Perform a Ledger Login Step-by-Step
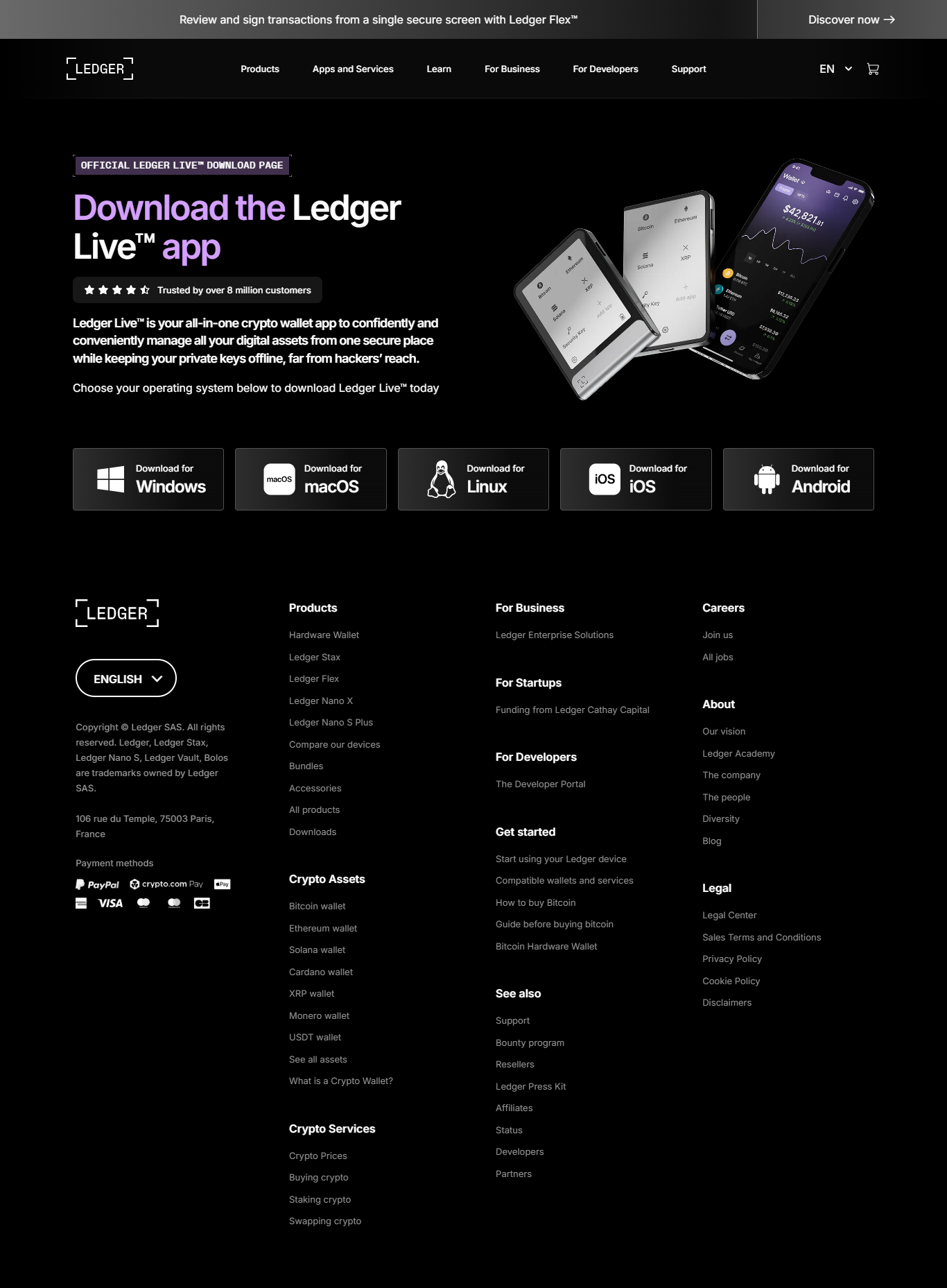
Step 1: Install Ledger Live
Download Ledger Live from the official Ledger website. This application is your gateway to manage your assets and connect securely with your Ledger hardware wallet.
Step 2: Connect Your Device
Plug in your Ledger Nano device via USB or pair it via Bluetooth if supported. The device should automatically connect to the Ledger Live app.
Step 3: Enter Your PIN
Use the buttons on your device to input your PIN code. This step ensures that only you can access your wallet—even if someone gets hold of your computer.
Step 4: Access the Dashboard
Once authenticated, your Ledger Live dashboard will load, displaying your crypto portfolio, balances, and management tools.
Why Ledger Login is the Safest Option for Crypto Holders
The Ledger login process is designed to mitigate every possible point of failure. Instead of relying on traditional usernames and passwords, Ledger integrates hardware authentication—meaning the private keys that control your funds never touch the internet. Even if your computer is infected with malware, your crypto remains safe inside the Secure Element chip embedded in your Ledger device.
Think of it as owning a high-tech vault. You can see and move your digital assets, but the keys to that vault never leave your hands.
🔐 Important Tip
Never share your recovery phrase. It’s the only backup of your wallet. Keep it written down and stored securely offline. Ledger will never ask for it under any circumstance.
Security Layers Behind Ledger Login
Ledger’s ecosystem is fortified by several advanced security mechanisms. Each login is a multi-layered process ensuring data integrity and user authentication.
| Security Layer | Description |
|---|---|
| Secure Element Chip | Stores your private keys in an isolated hardware environment resistant to physical attacks. |
| PIN Verification | Prevents unauthorized access even if your Ledger is stolen. |
| Firmware Integrity | Ensures only official, verified Ledger firmware runs on your device. |
| Offline Key Management | Your private keys never interact with the internet, reducing hacking exposure to zero. |
Troubleshooting Common Ledger Login Issues
- Device Not Recognized: Try another USB port or cable. If Bluetooth, ensure both devices are paired correctly.
- PIN Forgotten: Restore your wallet on a new device using your 24-word recovery phrase.
- App Not Syncing: Restart Ledger Live or reinstall the latest version to fix connectivity issues.
Ledger Login on Mobile Devices
Ledger Live Mobile offers the same security features as its desktop version, making it possible to manage your crypto safely on the go. For Bluetooth-enabled devices, always ensure your connection is private and avoid pairing in crowded or public networks. The mobile app lets you track balances, stake coins, and verify transactions without ever compromising your seed phrase.
💡 Pro Tip
Consider using Ledger’s “blind signing” feature to confirm transaction details directly on your device screen. It ensures you approve only what you see.
Ledger Login vs. Other Wallet Systems
| Feature | Ledger | Trust Wallet | Coinbase Wallet |
|---|---|---|---|
| Key Storage | Hardware (Offline) | Software (Online) | Cloud/Software |
| Security Level | High | Medium | Medium |
| Offline Access | Yes | No | No |
| Device Requirement | Ledger Hardware | None | None |
FAQs About Ledger Login
1. Can I use Ledger without logging in?
No. Accessing Ledger Live or performing any operation requires connecting and authenticating your Ledger device.
2. What happens if I lose my Ledger?
You can restore your funds on a new device using your recovery phrase. Always keep it offline and safe.
3. Is Ledger Login the same on desktop and mobile?
Yes, the security architecture is identical. The only difference lies in connectivity—USB for desktop, Bluetooth for mobile.
“With every Ledger login, you’re not just accessing your crypto—you’re defending your digital sovereignty.”
Conclusion: Ledger Login Protects What Matters Most
The Ledger login process exemplifies the highest standards in crypto security. It merges intuitive usability with cold-storage protection, giving users peace of mind that their digital assets are safe from online threats. Whether you manage Bitcoin, Ethereum, or DeFi tokens, your Ledger ensures that control remains firmly in your hands. Secure every login, verify every transaction, and embrace the confidence that true self-custody brings.